[ad_1]
When Apple dropped macOS Sequoia final month, it added new selections like window snapping and the flexibleness to administration your iPhone out of your Mac. Along with surface-level modifications, nevertheless, the mannequin new change furthermore launched a power assortment of patches for safety vulnerabilities. On account of it occurs, one among these vulnerabilities was found by none apart from Microsoft, and is form of regarding for Macs used inside organizations.
How Safari’s TCC flaw works
Microsoft described its findings in a weblog submit on Oct. 17, virtually one month after the Sept. 16 launch of macOS Sequoia. The corporate calls the flaw “HM Surf,” named after the teachable swap contained in the Pokémon assortment, which they found permits unhealthy actors to bypass Apple’s Transparency, Consent, and Administration platform for Safari. TCC typically ensures that apps with out applicable permission can’t entry companies like your location, digicam, or microphone. It’s vital for preserving your privateness from apps that may in each different case need to abuse it.
Nonetheless, Apple supplies just some of its personal apps entitlements that permit them to bypass these TCC roadblocks. It is Apple’s app, in the long run, so the corporate is aware of it is not malicious. In Safari’s case, Microsoft discovered the app has entry to your Mac’s type out e-book, digicam, and microphone, amongst utterly completely different companies, with out having to endure TCC checks first.
All that talked about, you proceed to come back throughout TCC checks whereas utilizing Safari all via web websites: That is what occurs once you load a web based net web page, and a pop-up asks should you will permit the location entry to not less than one issue like your digicam. These TCC settings per web site are saved to a listing in your Mac beneath ~/Library/Safari.
That is the place the exploit is on the market in: Microsoft found chances are high you will change this itemizing to a singular location, which removes the TCC protections. Then, chances are high you will modify delicate recordsdata throughout the exact dwelling itemizing, then change the itemizing as soon as extra, so Safari pulls from the modified recordsdata you set in place. Congratulations: You might be truly capable of bypass TCC protections, and take an image with the Mac’s webcam, together with entry location information for the machine.
Microsoft says there are a selection of actions unhealthy actors might possibly take from this occasion, together with saving the webcam image someplace they will entry it later; doc video out of your webcam; stream audio out of your microphone to an out of doors present; and run Safari in a small window, so you do not uncover its practice. Importantly, third-party browsers should not affected correct proper right here, as they need to cope with Apple’s TCC necessities, and have not bought Safari’s entitlements to bypass them.
Whereas Microsoft did uncover suspicious practice in its investigation that may degree out this vulnerability has been exploited, it couldn’t say for optimistic.
This vulnerability solely impacts MDM-managed Macs
After studying Microsoft’s report, ou may presumably be apprehensive regarding the prospect of unhealthy actors snooping in your Mac by way of Safari. Nonetheless, what won’t be made categorical correct proper right here is that this vulnerability solely impacts MDM-managed Macs, i.e. Macs belonging to organizations managed by a central IT service. That choices Macs issued to you out of your job, or a laptop computer belonging to your college.
Apple confirms as somewhat so much in its safety notes for macOS Sequoia, in a relatively short-term entry contemplating the privateness and safety implications:
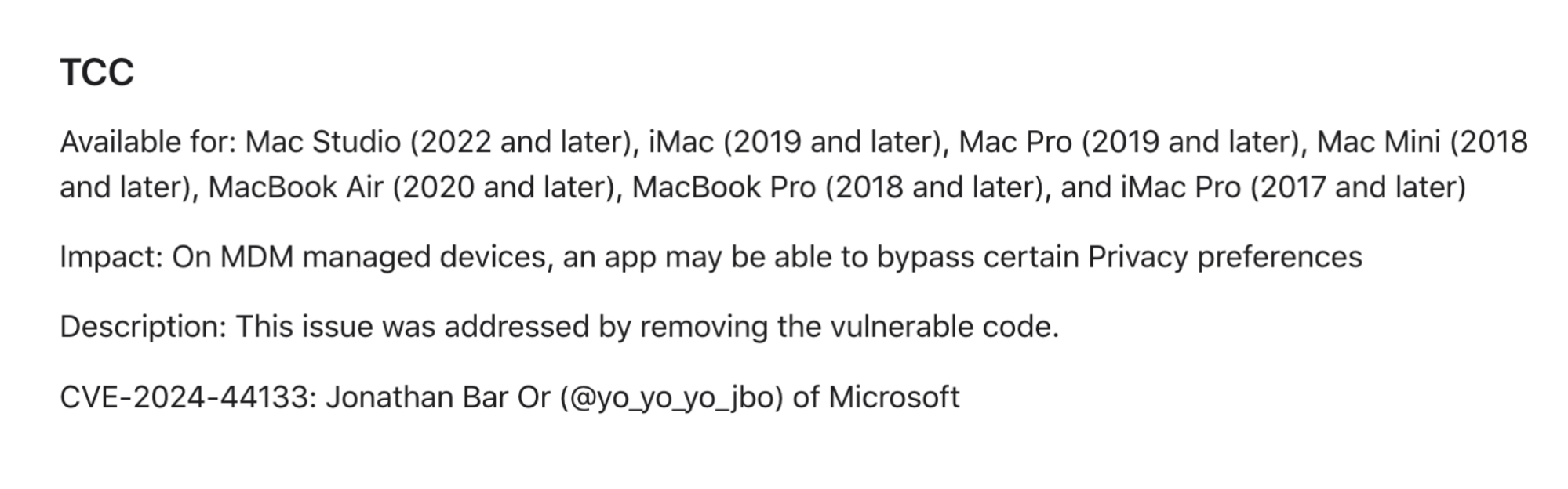 Credit score rating score: Apple
Credit score rating score: AppleIn any case, the flaw continues to be important, nonetheless it’s additional restricted. You wouldn’t must stress about Safari in your private Mac permitting hackers to entry your webcam, microphone, and web site. Nonetheless should you do have a Mac issued from work or college that’s MDM-managed, that might presumably be a precedence, and it is best to organize the change as quickly as attainable.
Patching the flaw in your MDM-managed Mac
This flaw impacts the following Macs: Mac Studio (2022 and later), iMac (2019 and later), Mac Expert (2019 and later), Mac Mini (2018 and later), MacBook Air (2020 and later), MacBook Expert (2018 and later), and iMac Expert (2017 and later).
It is attainable your group has already issued the change in your Mac, whether or not it’s eligible. Nonetheless, in case your machine won’t be working macOS Sequoia, research alongside alongside together with your company or college’s IT to see when an change will flip into obtainable.
[ad_2]















Leave a Reply